GSM & UMTS MSRN (Mobile Roaming Numbers) information and frauds
December 4, 2011 | Posted in News | By admin
Comments Off on GSM & UMTS MSRN (Mobile Roaming Numbers) information and frauds
MSRN information and frauds from Humbug Labs
http://www.humbuglabs.org/blog/2011/12/ring-ring-your-mobile-is-being-phreaked/
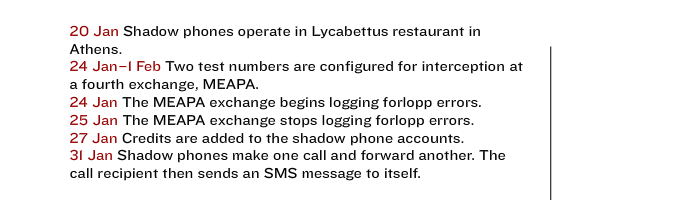
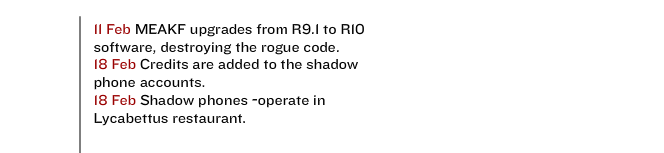
The Athens Affair – Ericsson AXE10 Mobile MSC backdooring & spying

June 29, 2007 | Posted in News | By admin
Comments Off on The Athens Affair – Ericsson AXE10 Mobile MSC backdooring & spying
“The prime minister of Greece was told that his cellphone was being bugged, as were those of the mayor of Athens and at least 100 other high-ranking dignitaries”.
“The victims were customers of Athens-based Vodafone-Panafon, generally known as Vodafone Greece.”
“Rogue software used the lawful wiretapping mechanisms of Vodafone’s digital switches to tap about 100 phones”.
“Like most phone companies, Vodafone Greece uses the same kind of computer for both its mobile switching centers and its base station controllers—Ericsson’s AXE line of switches.”
“In AXE exchanges a remote-control equipment subsystem, or RES, carries out the phone tap by monitoring the speech and data streams of switched calls. It is a software subsystem typically used for setting up wiretaps, which only law officers are supposed to have access to. When the wiretapped phone makes a call, the RES copies the conversation into a second data stream and diverts that copy to a phone line used by law enforcement officials.
Ericsson optionally provides an interception management system (IMS), through which lawful call intercepts are set up and managed. When a court order is presented to the phone company, its operators initiate an intercept by filling out a dialog box in the IMS software. The optional IMS in the operator interface and the RES in the exchange each contain a list of wiretaps: wiretap requests in the case of the IMS, actual taps in the RES. Only IMS-initiated wiretaps should be active in the RES, so a wiretap in the RES without a request for a tap in the IMS is a pretty good indicator that an unauthorized tap has occurred. An audit procedure can be used to find any discrepancies between them.”
“From time to time the intruders needed access to the rogue software to update the lists of monitored numbers and shadow phones. These activities had to be kept off all logs, while the software itself had to be invisible to the system administrators conducting routine maintenance activities. The intruders achieved all these objectives. They took advantage of the fact that the AXE allows new software to be installed without rebooting the system”
“The investigators examined the dumps more thoroughly and found the rogue programs. What they found though, was in the form of executable code—in other words, code in the binary language that microprocessors directly execute. Executable code is what results when a software compiler turns source code—in the case of the AXE, programs written in the PLEX language—into the binary machine code that a computer processor executes. So the investigators painstakingly reconstructed an approximation of the original PLEX source files that the intruders developed. It turned out to be the equivalent of about 6500 lines of code, a surprisingly substantial piece of software.”
Source & More information: The Athens Affair – IEEE Spectrum.